THE SIMPLE ENTREPRENEUR
ENTREPRENEUR | BUSINESS | FAMILY | FITNESS | HEALTH | LIFE
Hello. My name is Marco Tran (aka The Simple Entrepreneur) and I am an entrepreneur based in Sydney Australia. I was born in Vietnam, grew up in Italy and currently residing in Australia. My passion is in the digital space and I have launched several digital products. You will find these on the portfolio page. I started this website so I could leave a digital footprint of my random thoughts, ideas and life in general. I hope this website can be an inspiration and help you in your own journey in the digital space.
Major Milestones
Featured Posts
Featured posts you may be interested in
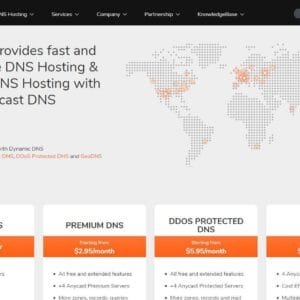
FEATURED TOOLS I USE
Tools that I use and recommend
Portfolio
Some of the websites, businesses, products and ideas I have launched
Latest Blog Posts
The art of words is to never stop writing
If you are using Microsoft Exchange Online and you try to forward messages from a mailbox or shared mailbox to an external email address, you may run into a frustrating delivery failure. The message usually looks something like this: Remote server returned access denied. Your organisation does not allow external...
Running local AI models has become a lot more practical than it was even a short time ago. What used to feel like something only large companies or highly technical teams could do is now something a solo operator, content creator, small business owner, or curious tech user can start...
This was one of those simple little products that immediately made me think, why did I not start using these earlier, because cable ties are one of the most useful things to keep around the house, the office, the car, the garage, and even in a travel bag, but the...
There is something quite satisfying about testing a simple accessory that solves a very specific everyday problem, especially when it is the kind of problem you only really notice after using standard cables for a long time. A normal charging cable does the job, but the moment you start using...
Small accessories like a USB adapter do not usually get much attention until the moment you actually need one, and that is why devices like this 8 in 1 adapter can be more useful than they first appear. If you are working across different devices, transferring files, charging a phone,...
If you are using a DEYE hybrid inverter and you have opened the app to adjust export settings, there is a good chance you have noticed something slightly frustrating straight away. Inside the normal settings area, the max sell power field appears to have a lower limit of 500 watts,...
Contact Me
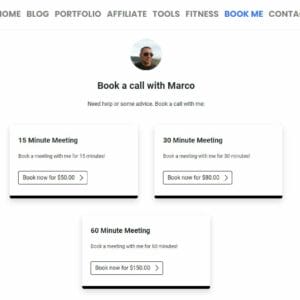
I’m very approachable and I’m more than happy to answer any of your questions. So, just send me a message and I’ll try to respond to you as soon as I can. You can also follow me on any of the social media platforms below. If you need help, you can also book me: